There are numerous tools that can be utilized to identify and minimize the impact of DDOS attacks. In this article, we’ll look at RUDY, Anycast, SolarWinds Security Event Manager and Imperva. These tools will help you protect your Network cdn (https://cannabisconnections.com/) from attacks that target both the application and network layers. Continue reading to find out more! We’ll also explain how they function and what can expect.
RUDY
 The RUDY attack is an DDoS attack which exhausts the server’s connection tables with a small volume of traffic. This makes the targeted server crash. It exploits a flaw in the HTTP protocol. This is particularly effective against websites that use web forms. This tool can be used together with other tools, for instance, the OWAS DDOS URL POST simulator. The OWAS DDOS HTTP Post is a powerful mitigation tool that simulates an attack by DDOS.
The RUDY attack is an DDoS attack which exhausts the server’s connection tables with a small volume of traffic. This makes the targeted server crash. It exploits a flaw in the HTTP protocol. This is particularly effective against websites that use web forms. This tool can be used together with other tools, for instance, the OWAS DDOS URL POST simulator. The OWAS DDOS HTTP Post is a powerful mitigation tool that simulates an attack by DDOS.
When a web form user transmits data to a server, legitimate users will transmit the data in one or two packets. The server shuts down the connection. An attacker may utilize a tool called RUDY, that spreads data across several packets to make the server wait for each packet. This could lead to the website being shut down. This tool also blocks web servers from responding user requests.
RUDY DDOS simulator is an excellent way to test the security of your server. DDOSIM simulates an application layer DDOS attack by creating fake hosts and attacking the servers with layer 7. Then, it assesses the response of the security framework. It runs on LINUX and is a free tool and functions optimally on this platform. It simulates a variety of attacks that can aid in understanding the thought process of hackers.
RUDY attacks differ from traditional mitigation methods. They are focused on keeping a website server intact. Their slow and low-and-slow strategy is designed to exhaust a web server’s resources but still appear like legitimate traffic. In the event, the victim’s primary server may become unavailable, resulting in the possibility of a DDoS attack. You can find mitigation solutions for R.U.D.Y. RUDY , it’s a good idea to be on the radar for DDoS attacks.
Anycast
IP anycast offers two distinct advantages for DDoS attacks. First the distributed traffic generated by multiple servers helps spread the burden from a single attack. In addition, anycast can make the service withstand a DDoS attack even if a single server fails. If a single server fails, all the neighboring Anycast servers may fail if they do not have reserve capacity. The entire service could crash.
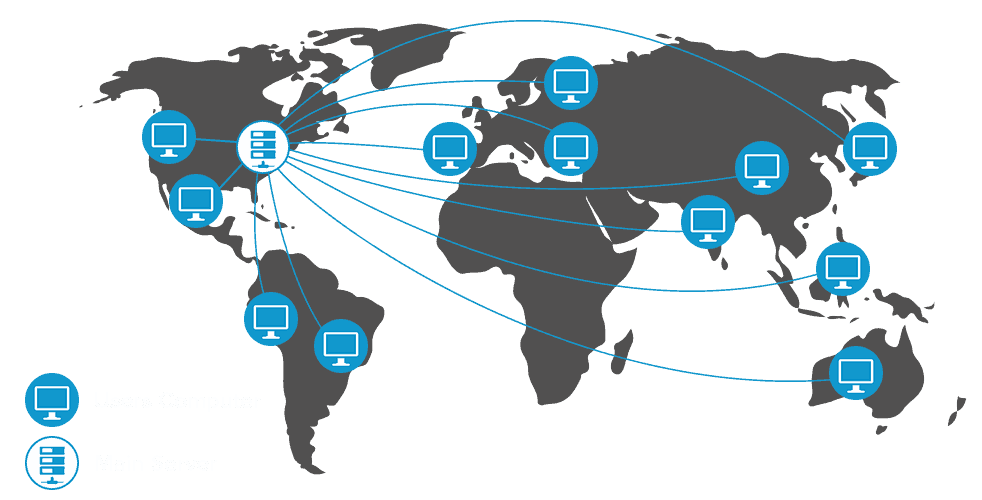
IP anycast is a popular service that offers essential internet-related services throughout the world. It increases redundancy and decreases the impact of DDoS attacks by making the targeted service unavailable to a tiny number of users. To defend against attacks it can be optimized either statically or CDN services dynamically. Anycast generally increases the capacity of multiple sites. This allows each site’s catchment to keep an attack at bay and to maintain the availability of legitimate users.
Anycast helps reduce latency and respond time, leading to a quicker loading time and satisfied customers. It also boosts site availability by balancing users across multiple nodes. It also strengthens DDoS defenses and allows users to reach the website from any other location. A survey conducted by anycast and DDoS mitigation software revealed that 96% of all websites online were affected by DDoS.
Anycast allows CDNs to be more resistant to distributed denial of service attacks. Anycast reduces the number of hops required to process requests by displaying individual IP addresses across multiple servers. As a result, the network is able to withstand top cdn providers high traffic, network congestion, and DDoS attacks. It can also decrease network latency, routing traffic to the nearest site. This configuration simplifies server configuration and also offers redundancy.
SolarWinds Security Event Manager
Many DDoS mitigation tools are available on the market. SolarWinds Security Event Manager, for instance is a solution for software that analyzes and monitors security alerts in real-time. Previously known as Log & Event Manager this software is able to detect DDoS attacks, and makes use of cyber-threat Intelligence to block blacklisted IPs. It also targets the Botnet’s Command & Control Center. It’s available for download free for a 30-day trial.
DDoS attack mitigation tools monitor the IP and port numbers for attackers and record the attacks to allow you to look them up retrospectively. SolarWinds SEM logs are viewed in a logical format with the help of built-in connectors. It is simple to use, and comes with search options that let you filter by IP addresses or time. It is easy to pinpoint the root of any DDoS attack by using simple Boolean logic and then analyze it.
While some companies have spent thousands of dollars on DDoS mitigation tools, SolarWinds Security Event Manager is a relatively inexpensive but a powerful SIEM tool. SolarWinds Security Event Manager comes with event log monitoring capabilities that let you see the websites that receive a lot of traffic. SolarWinds SEM also has automated features that can detect DDoS attacks in real time. The tool can be set up to study the logs of traffic on networks and look for anomalies.
You can also make use of IP Stresser to test the strength of your servers and Network CDN Global (https://cannabisconnections.com/). It can reach up to 313 users per day and is free for MS and EIISAC members. CIS Benchmarks also offers a DDoS mitigation tool called Advanced IP Scanner, which is free for MS and EI-ISAC members.
SolarWinds Security Event Manager also provides a free WAN killer Traffic Generator it is a feature-rich toolkit to stress test medium-sized businesses. The test servers are located in a nation that is not identifiable by IP addresses. This tool simulates botnet activity by sending attacks to a certain IP address. It also includes HULK, a Denial of Service (DoS) attack tool. This tool is used to attack websites with distinctive traffic volume.
Imperva
Your website is protected from massive DDoS attacks with Imperva DDoS mitigation tools. The TTM mitigates attacks within three seconds or less regardless of the attack’s size or duration. In addition the service’s SLA guarantees quick and automated DDoS action and protects against attacks of any method. We’ll discuss the company’s history of producing results.
Imperva’s DDoS protection software filters traffic and applies DDoS protection solutions to the network. Only traffic that is filtered is permitted to reach your hosts. This protects your content delivery network cdn infrastructure, software, cdn worldwide and hardware and ensures business continuity. Moreover, it uses a constantly updated, extensive DDoS threat database to identify new attack methods and apply remediation in real-time to all websites that are protected.
Imperva DDoS mitigation tools assist to secure websites and networks from massive DDoS attacks. They safeguard DNS servers, individual IP addresses, and entire networks. Imperva helps minimize the financial and operational losses caused by these attacks by making sure your online business operates at its best. The solution also helps reduce the damage to your reputation. It is essential to comprehend the capabilities of Imperva DDoS mitigation software to safeguard your online business from these attacks.
The Imperva DDoS mitigation tool protects against the most popular DDoS attacks. Its sophisticated technology utilizes an extensive global scrubbing system of 49 PoPs in order to distinguish legitimate traffic from malicious bots. Imperva also employs machine learning and automation to identify and mitigate large-scale attacks within three seconds. With its 9 Tbps global cdn network, Imperva can mitigate 65 billion attack packets per second that is a high rate.
